Installation Guide for Cisco Identity Services Engine (ISE)
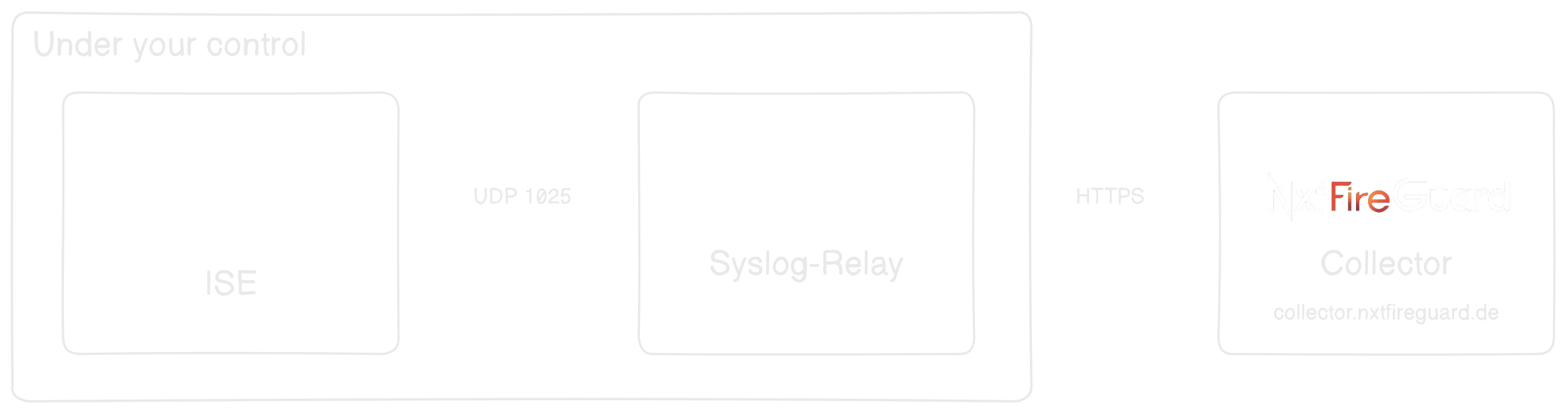
Cisco ISE does not natively support sending authentication logs to an HTTP destination. To address this limitation, we will use a syslog Forwarder. The setup is illustrated below:
1. Prerequisites
System Requirements
- ✅ Virtual Machine:
- 2 CPU Cores
- 4 GB RAM
- 20 GB Hard Disk
- 1x Network Interface
- ✅ Valid NxtFireGuard License Key
2. Install Ubuntu or Debian Server OS
Ensure you have the latest version installed before proceeding.
3. Download NxtFireGuard Threat Log Forwarder
-
Visit NxtFireGuard GitHub Releases.
-
Download the latest release as a
.zipor.tar.gzfile:wget <latest-release> -
Extract the downloaded archive:
tar -xf <download> -
Navigate to the extracted directory:
cd NxtFireGuard-Threat-Log-forwarder
4. Installation
- Grant execution permissions to the installation script:
chmod +x install.sh - Run the installation script with superuser privileges:
sudo ./install.sh - Follow the on-screen prompts:
- Enter your License Key: (Available in Account Dashboard)
[your_license_key]: 4WPHKY3K-9RWJXKD3-VKLAUG96-E7N7ALMF - Assign a name to your Threat-Log-Forwarder:
[forwarder-name]: nfg-threat-log-fwd-01 - Enable integration with Cisco-FMC and/or Cisco-ISE?
(true/false) [false]: true - Enable Logstash integration with T-Pot?
(true/false) [false]: false
- Enter your License Key: (Available in Account Dashboard)
5. Post-Installation Steps
After installation, log out and back in to apply changes. Start the service:
systemctl start nfg-threat-forwarder.service
6. Managing the Service
Control the service using the following commands:
systemctl status nfg-threat-forwarder.service # Check service status
systemctl start nfg-threat-forwarder.service # Start the service
systemctl stop nfg-threat-forwarder.service # Stop the service
systemctl restart nfg-threat-forwarder.service # Restart the service
7. Configuration Management
Modify settings in the .env file and restart the service:
systemctl restart nfg-threat-forwarder.service
For nfg-syslog container configuration, update syslog/syslog-ng.conf:
vim syslog/syslog-ng.conf
Replace X_LICENSE_KEY with your actual key:
@define X_LICENSE_KEY "YOUR-LICENSE-KEY"
Next Steps
Configuring Log Forwarding from ISE to the Container
To forward AAA Audit Logs from Cisco ISE to the Log Relay Server, follow Cisco's official documentation. Ensure that logs are sent to UDP port 1025.
Once configured, proceed to the Adding a Host section to verify the connection.
For assistance, reach out to our team via the Contact Form.